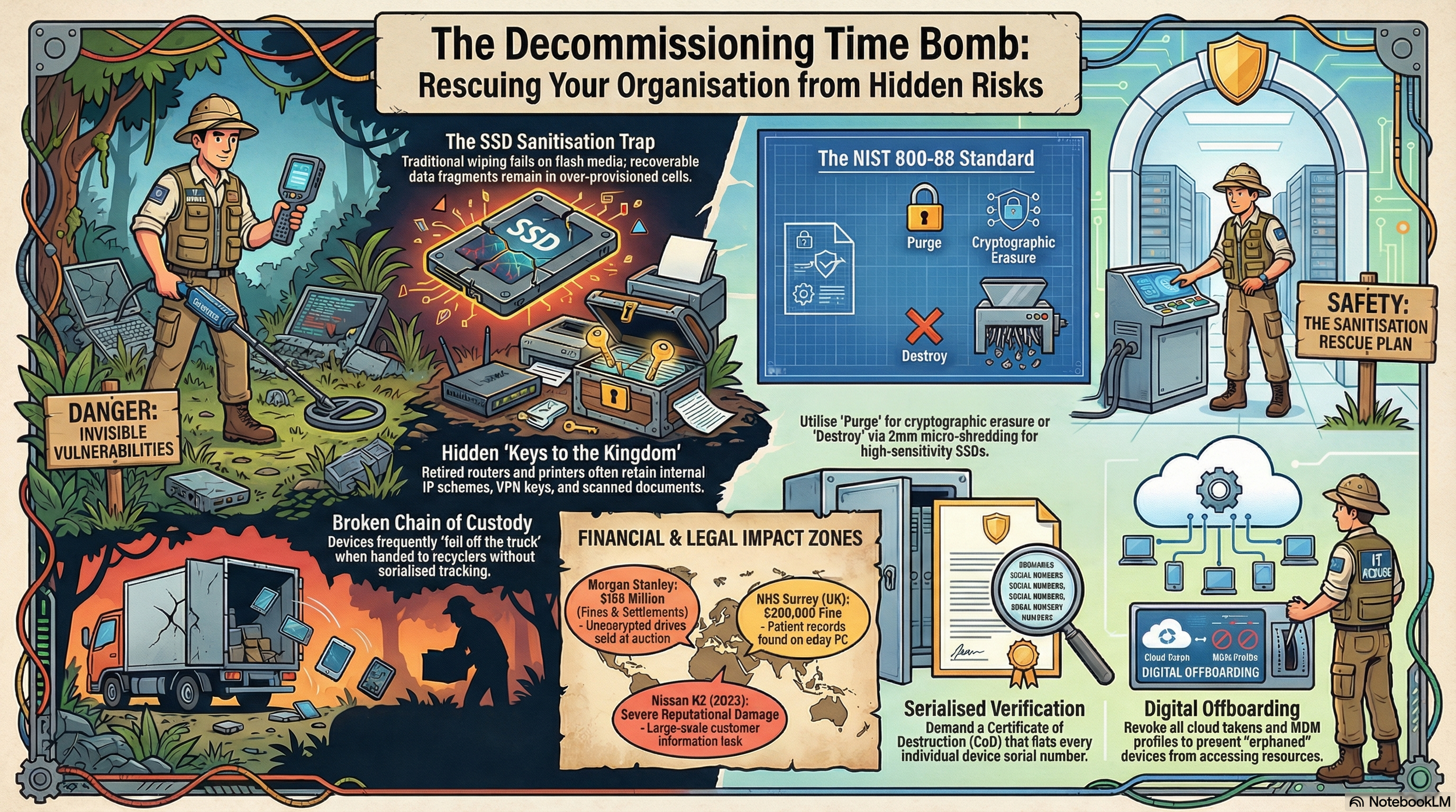
5 Hidden Dangers in the "Forgotten" Stage of IT
The Security Gap No One Is Watching
In the world of enterprise security, we are obsessed with the "active" state. We invest billions in next-generation firewalls, zero-trust architectures, and real-time endpoint detection to guard data while it lives on our networks. Yet, there is a "forgotten" stage of the technology lifecycle where these formidable defenses simply evaporate: IT asset decommissioning.
While active systems are shielded by layers of encryption and monitoring, retired hardware frequently transitions into a security vacuum. Devices containing decades of intellectual property and sensitive "data remanence" often sit in unlocked basements, unsecured storage rooms, or on loading docks awaiting pickup by third-party logistics firms. This "last mile" of IT is not a logistical checkbox; it is a high-stakes security operation. Without a rigorous strategy, your retired hardware becomes a potential "time bomb" of liability, holding onto secrets long after you believe they have been purged.
1. Your Shredder Might Be Failing Your SSDs
A primary strategic error in modern decommissioning is failing to account for the physical divergence between Hard Disk Drives (HDDs) and Solid State Drives (SSDs). Traditional HDDs store data magnetically and can be neutralized via degaussing. However, as of 2024, the dominance of flash-based media has rendered degaussing an obsolete tactic.
SSDs and NVMe devices utilize complex flash memory algorithms—specifically wear-leveling and over-provisioning—to extend drive life. These processes map logical addresses to physical cells in a way that standard software-based wiping or "formatting" cannot see. Forensic tools can easily bypass the operating system to access the underlying bits. Furthermore, because flash memory chips are smaller than a thumbnail, standard industrial shredders that produce coarse strips are ineffective. A single surviving chip can be extracted with minimal effort by a sophisticated actor using hardware forensics to recover gigabytes of data.
The Gold Standard of Physical Destruction: For flash-based media, organizations must shift from coarse shredding to pulverization or disintegration. To ensure data is unrecoverable, the media must be reduced to a particle size of 2mm or less. For logical sanitization, the preferred method is Cryptographic Erasure (CE), which leverages internal encryption-at-rest to destroy access keys, rendering the data instantly irrecoverable.
2. The "Filing Cabinet" in the Breakroom (Printer & IoT Risks)
Vulnerabilities extend far beyond servers to the peripheral "edge" of the network. Multifunction Printers (MFPs) and Internet of Things (IoT) devices represent massive, often overlooked data hazards. For the last 22 years (since approximately 2002), enterprise-grade MFPs have been manufactured with internal hard drives that store digital images of every document scanned, copied, or printed. When these devices are returned at the end of a lease or sold second-hand, they essentially act as unsecured filing cabinets.
Furthermore, these peripherals and IoT devices—such as smart thermostats or VoIP phones—utilize NVRAM (Non-Volatile Memory) to store contact lists, call logs, and network credentials. Relying on a "Factory Reset" is a dangerous gamble; these resets often clear user preferences but leave cached network SSIDs and passwords in plain text within the NVRAM.
The irony is sharp: an organization can spend millions on perimeter defense only to be breached via a second-hand copier bought for $300 or a smart thermostat in a lobby fish tank. In one documented case, attackers used a connected thermostat as a backdoor to move laterally through a network and exfiltrate 10 gigabytes of data.
3. There is No Expiration Date on Liability: The Morgan Stanley Lesson
Treating IT Asset Disposition (ITAD) as a "cost-saving logistics exercise" rather than a security function is a catastrophic strategic mistake. The Morgan Stanley case study (2016–2019) remains the definitive warning: the firm hired a moving company with no specialized data destruction expertise to decommission two data centers.
Because the firm failed to ensure Full-Disk Encryption (FDE) was active as a final line of defense and relied on a non-specialized vendor, thousands of unencrypted hard drives containing the personal information of 15 million customers were sold on auction sites with data intact. This process failure resulted in $163 million in total fines and legal settlements.
The Time Bomb of Risk: There is no expiration date on liability in ITAD. This breach surfaced years after the equipment left the firm's control. Once hardware leaves your facility, any failure in the decommissioning process becomes a permanent, unguided risk that can detonated at any time.
4. The "Ghost in the Cloud" (Orphaned Connections)
In our hybrid-cloud era, decommissioning is no longer just physical; it is a digital offboarding process. A major vulnerability is "Incomplete De-provisioning," where retired hardware retains its "digital keys to the kingdom."
When a physical device is retired, it must be systematically removed from Mobile Device Management (MDM) profiles and its access revoked at the infrastructure level. If an organization fails to update Certificate Revocation Lists (CRLs)or OCSP responders, the physical device remains a persistent skeleton key. Unauthorized possessors can use these "orphaned" connections to bypass perimeter security and access corporate cloud resources.
Beyond the device identity, retired hardware often contains "shadow data" in hidden application folders and configuration metadata, including:
VLAN structures and internal IP schemes.
VPN pre-shared keys.
Browser cookies and saved API tokens.
5. The "Chain of Custody" is the Weakest Link
The most dangerous moment in the ITAD lifecycle is the "hand-off." Without a secure, serialized chain of custody, devices can "fall off the truck" unnoticed. You cannot securely decommission what you haven't tracked; an asset that disappears without a record is a data breach in progress.
Organizations must move from a disposal mindset to a Sanitization and Verification mindset. This requires a professional distinction between Verification (confirming a specific drive was wiped) and Validation (the overall audit of the process).
To secure the chain of custody, strategists must:
Implement Serialized Inventory: Track every device by serial number from the desk to the point of final destruction.
Demand Granular CoDs: Refuse bulk receipts. Accept only Certificates of Destruction (CoD) that list individual serial numbers for every drive processed.
Audit the Auditor: Conduct annual spot checks of your vendor’s facility to ensure drives aren't sitting in an unsecured warehouse.
Beyond the Shredder
The landscape of ITAD is shifting toward "Sanitisation Assurance." We are entering an era where manual tracking is being replaced by AI-driven platforms and blockchain technology to create immutable chain-of-custody records.
The regulatory bar is also rising. In September 2025, NIST released SP 800-88 Revision 2, shifting the focus from simple technical "how-to" instructions to the establishment of comprehensive, enterprise-wide media sanitization programs. This update emphasises the need for whole-media sanitization to avoid "spilling" data into over-provisioned areas of modern storage.
As you evaluate your organisation's "last mile" of security, ask yourself: Is your data truly gone, or is it just waiting for the right person to find it in an eBay listing? The difference between a routine retirement and a $163 million disaster lies in the technical rigour of your decommissioning process.