The Ghost in the Machine
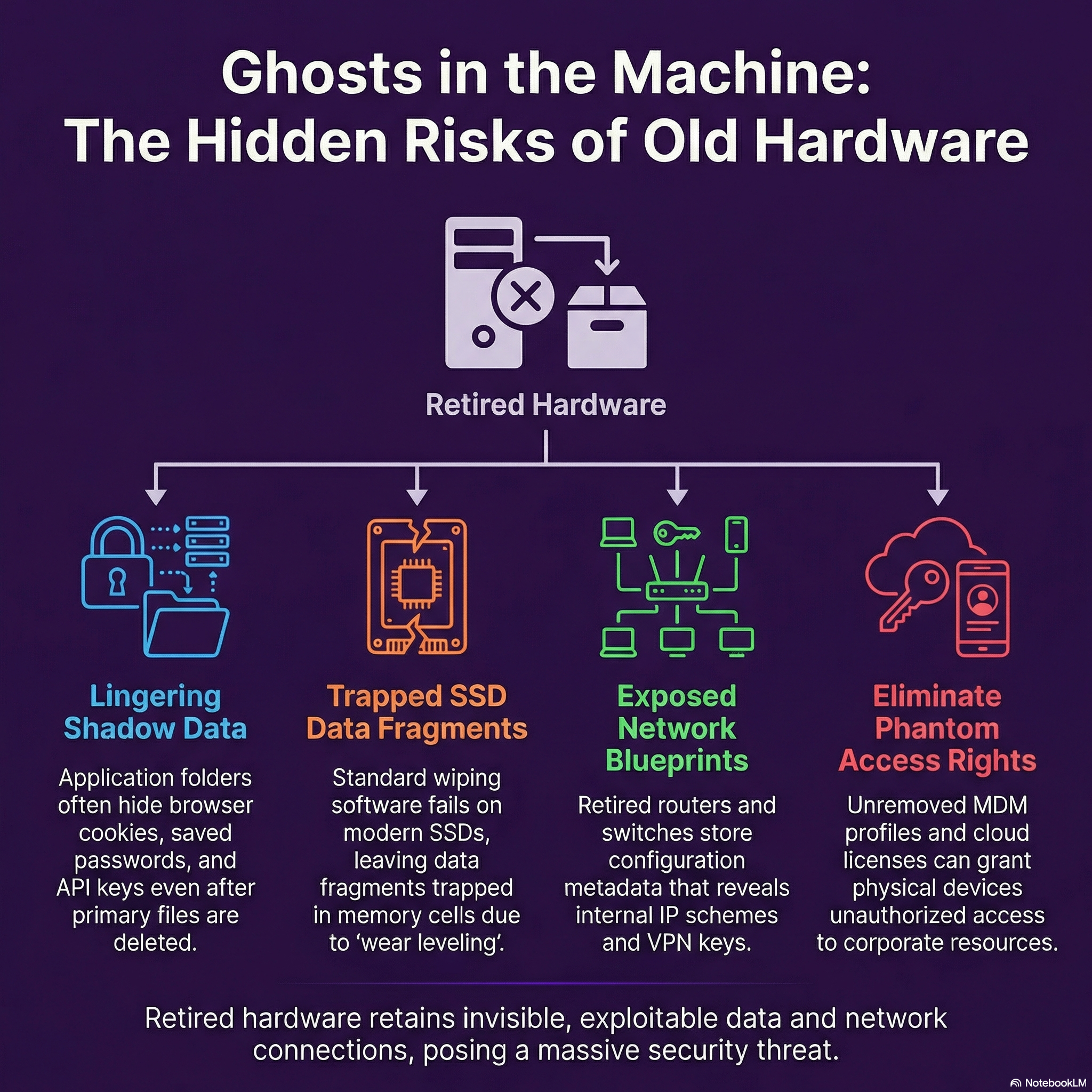
Here are the primary ways these "ghosts" manifest in decommissioned hardware:
• Lingering "Shadow Data": Even after primary files are deleted, "shadow data" such as browser cookies, saved passwords, and API keys frequently remain hidden deep within application folders.
• Hidden Memory in Peripherals: It is not just computers that hold sensitive data. Devices like printers, VoIP phones, and smart IoT devices contain Non-Volatile Memory (NVRAM) that secretly stores contact lists, call logs, and even cached copies of scanned documents.
• Trapped Data Fragments: Traditional "magnetic wiping" is often ineffective on modern Solid State Drives (SSDs). Because SSDs utilize a process called "wear leveling," data fragments can remain trapped in memory cells that standard software-based wipers simply cannot reach

5 Hidden Dangers in the "Forgotten" Stage of IT
Maintaining a secure chain of custody is extremely important to your cybersecurity because the physical hand-off of retired IT equipment to a disposal vendor is considered one of the most dangerous moments in an asset's lifecycle. Even the most sophisticated technical data-wiping methods are useless if poor process management allows the physical asset to be lost or stolen before it is actually sanitised.

Why Your Hardware Strategy is Quietly Draining Your Profits
Outsourcing Device Lifecycle Management (DLM) transforms IT from a complex, reactive internal burden into a streamlined external service. By shifting from an asset ownership model to a service-based utility, Small and Medium Enterprises (SMEs) can access enterprise-grade technology and expertise without the need for enterprise-level budgets or staff.
